The distributed denial-of-service (DDoS) attack is a malicious attempt to disrupt the target’s services by flooding the resource capacity of the server with high Internet traffic.
It is very crucial to detect such abnormal traffic and block the IP addresses of the attack source automatically to prevent the server from reaching its capacity.
In this article, you will learn how to protect a website running on the Apache webserver from DDoS, Bruteforce, and similar types of malicious attacks.
Here, we install and configure the mod_evasive which is an Apache module to protect the website from DDoS attacks.
Installing the mod_evasive Module of Apache
First of all, install the Apache web server utility package:
> sudo apt install apache2-utilsNext, install Apache’s mod_evasive module:
> sudo apt-get install libapache2-mod-evasiveThis will also install the postfix package. Here, you would need to select “Internet Site”.
Postfix is a mail transfer agent for delivering an email. In this case, we need postfix to notify via email whenever the mod_evasive module blocks the attacker’s IP address.
In case you don’t how to configure postfix, then you can read our guide on installing and configuring postfix for sending emails.
After installation of the mod_evasive module, you can check if it’s running:
> sudo apachectl -M | grep evasiveAfter running the above command, you would see the output as follows:
evasive20_module (shared)Now, we can move to the configuration of the mod_evasive module.
Configuring mod_evasive to Prevent DDoS Attacks
After installing the mod_evasive module, we need to edit its configuration file:
> sudo nano /etc/apache2/mods-enabled/evasive.confHere, you will see a block of lines:
<IfModule mod_evasive20.c>
#DOSHashTableSize 3097
#DOSPageCount 2
#DOSSiteCount 50
#DOSPageInterval 1
#DOSSiteInterval 1
#DOSBlockingPeriod 10
#DOSEmailNotify you@yourdomain.com
#DOSSystemCommand "su - someuser -c '/sbin/... %s ...'"
#DOSLogDir "/var/log/mod_evasive"
</IfModule>Now, we need to uncomment some of these lines by removing the “#” symbol.
Also, we increase DOSPageCount from 2 to 7, DOSSiteCount from 50 to 100, and DOSBlockingPeriod from 10 to 60.
The DOSSiteCount value of 50 is too aggressive and may lead to a false positive. This depends on your website traffic. You can always experiment with this value.
DOSPageCount is a limit for the number of requests for the same page in an interval of DOSPageInterval that is 1 second by default.
DOSSiteCount is a limit for the total number of requests for the same site in an interval of a number of seconds that is DOSSiteInterval (1 by default).
DOSPageCount and DOSSiteCount are the two important parameters that you may want to change. These two values should be less aggressive so the users don’t get blocked unnecessarily.
After the changes, it will look as follows:
<IfModule mod_evasive20.c>
DOSHashTableSize 3097
DOSPageCount 7
DOSSiteCount 100
DOSPageInterval 1
DOSSiteInterval 1
DOSBlockingPeriod 60
#DOSEmailNotify you@yourdomain.com
#DOSSystemCommand "su - someuser -c '/sbin/... %s ...'"
DOSLogDir "/var/log/mod_evasive"
</IfModule>Note that we have uncommented “DOSLogDir“, so we will need to create a new directory to store the logs.
To create the log directory, run the “mkdir” command as follows:
> sudo mkdir /var/log/mod_evasiveAlso, we will need to change its ownership to “www-data”.
> sudo chown -R www-data:www-data /var/log/mod_evasiveFinally, restart the Apache server for new changes to come into place.
> sudo systemctl restart apache2Testing Apache mod_evasive Module Against DDoS
Now, to test the configuration, there is a built-in test script that we can utilize. This script is already included in the mod_evasive module.
Open the test script file in the nano editor.
> sudo nano /usr/share/doc/libapache2-mod-evasive/examples/test.plHere, you will see the following line:
print $SOCKET "GET /?$_ HTTP/1.0\n\n";Replace the above line with:
print $SOCKET "GET /?$_ HTTP/1.0\r\nHost: 127.0.0.1\r\n\r\n";After replacing this line, you can save the file (Ctrl + X and Y). Then, run the script using the Perl command as follows:
> sudo perl /usr/share/doc/libapache2-mod-evasive/examples/test.plThis will replicate a simple DDoS attack. Now, if everything works correctly, then you would see the 403 response.
...
HTTP/1.1 403 Forbidden
HTTP/1.1 403 Forbidden
HTTP/1.1 403 Forbidden
...Also, to receive an email when an IP gets blocked, you can uncomment DOSEmailNotify and set your email in there.
For emails to work, you must configure the postfix correctly.
Every time you make any changes to the mod_evasive configuration file, always restart the Apache server in order to reload the new configuration.
You can find all the IPs that got blocked for 60 seconds temporarily in the log directory.
> sudo ls /var/log/mod_evasiveAlso, for testing purposes, you may continuously refresh any of your website pages to check if that will block you for 60 seconds after making several attempts.
Mainly, you can adjust the value of DOSSiteCount and DOSPageCount to higher or lower depending on your website traffic.
Note: If you want to temporarily disable Apache’s mod_evasive module, you can simply run the following command:
> sudo a2dismod evasiveSimilarly, to enable the mod_evasive module, you can run the following command:
> sudo a2enmod evasiveIn both cases make sure to restart the Apache server for changes to come into effect.
> sudo service apache2 restartIf you face an issue in setting up and configuring the mod_evasive module of Apache, then you may send your message to us via our contact form.
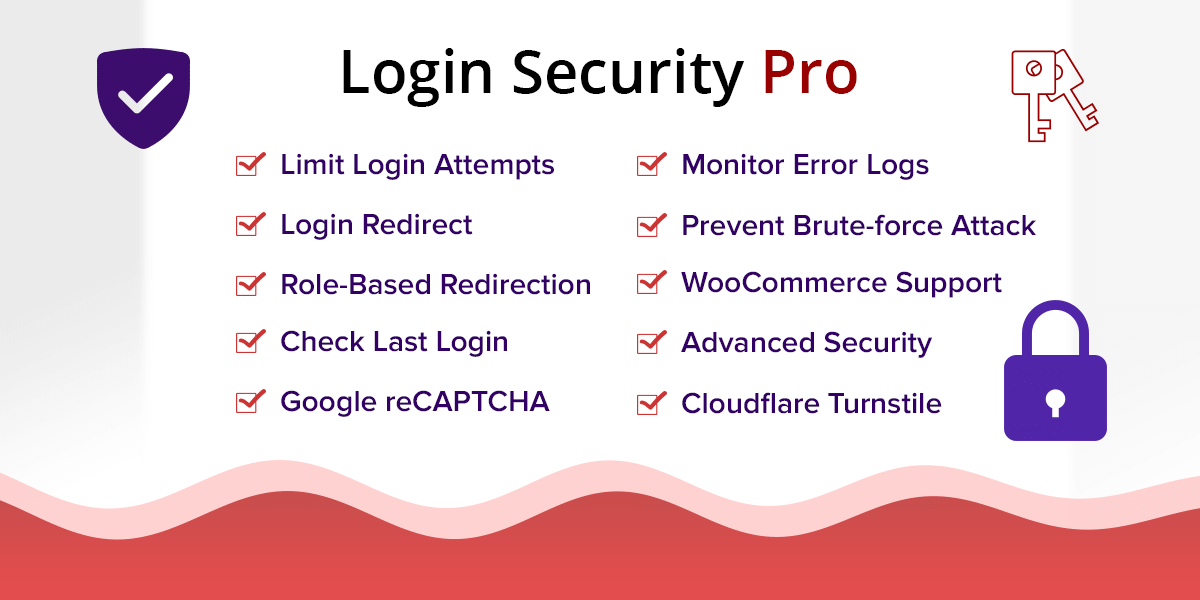
Furthermore, if you have a WordPress website, then you may also want to install and activate a captcha plugin to secure all the standard WordPress forms like the login form, etc.